Jakarta, odishanewsinsight.com – SIEM platforms (Security Information and Event Management) are essential tools for organizations seeking to enhance their cybersecurity posture. These platforms provide real-time analysis of security alerts generated by applications and network hardware, enabling organizations to detect, respond to, and mitigate potential threats. This article explores the key features of SIEM platforms, their benefits, evaluation criteria, and best practices for successful deployment.
What Are SIEM Platforms?
1. Definition and Purpose
SIEM platforms are integrated solutions that aggregate, analyze, and manage security data from across an organization’s IT infrastructure. They collect log and event data generated by servers, network devices, domain controllers, and more, allowing security teams to monitor and respond to incidents effectively.
2. Core Functions of SIEM Platforms
- Data Collection: SIEM platforms collect logs and events from various sources, providing a centralized view of security-related data.
- Normalization: The collected data is normalized to ensure consistency, making it easier to analyze and correlate events.
- Correlation: SIEM platforms analyze data to identify patterns and relationships between different events, helping to detect potential security incidents.
- Alerting: When suspicious activities are detected, SIEM platforms generate alerts to notify security teams for further investigation.
- Reporting: SIEM solutions provide reporting capabilities to help organizations meet compliance requirements and assess security posture.
Benefits of SIEM Platforms
1. Enhanced Threat Detection
By correlating data from multiple sources, SIEM platforms improve the ability to detect threats that may go unnoticed by traditional security measures. They can identify complex attack patterns and provide insights into potential vulnerabilities.
2. Faster Incident Response
SIEM platforms facilitate quicker incident response by providing security teams with real-time alerts and context about security events. This enables organizations to act swiftly to contain and mitigate potential threats.
3. Compliance and Reporting
Many industries have regulatory requirements that mandate monitoring and reporting on security events. SIEM platforms help organizations meet these compliance obligations by providing detailed logs and reports.
4. Centralized Security Management
SIEM platforms centralize security data from various sources, simplifying security management and reducing the complexity of monitoring multiple systems.
Evaluating SIEM Platforms
When evaluating SIEM platforms, organizations should consider several key criteria:
1. Scalability
The SIEM solution should be able to scale with the organization’s growth. It should handle increasing data volumes and adapt to changing security needs without compromising performance.
2. Integration Capabilities
A good SIEM platform should integrate seamlessly with existing security tools and infrastructure, such as firewalls, intrusion detection systems, and endpoint protection solutions.
3. User-Friendly Interface
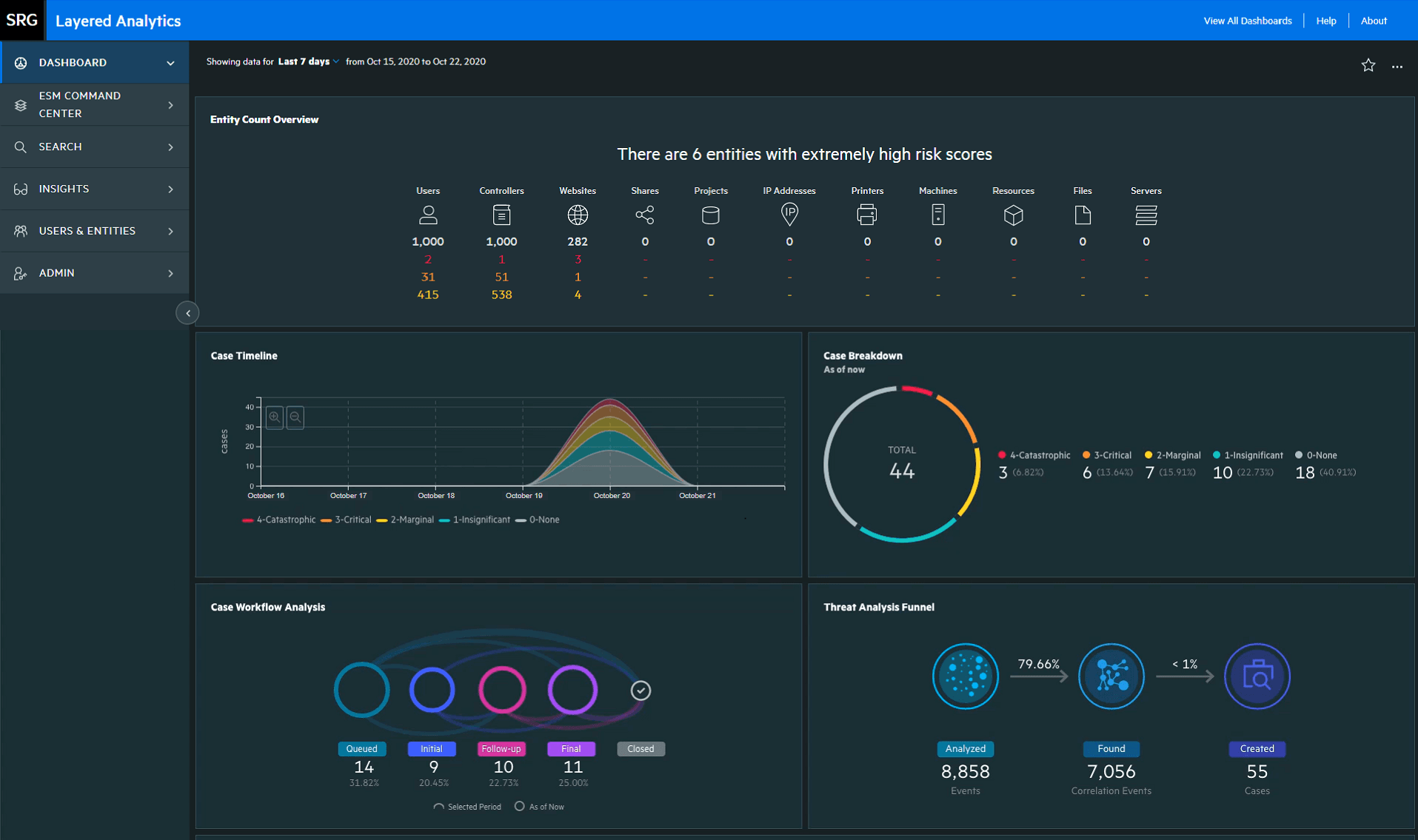
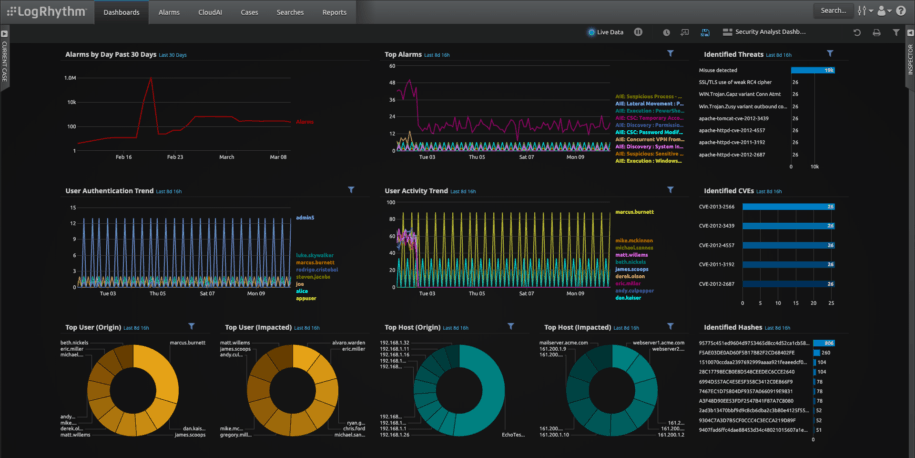
The platform should have an intuitive interface that allows security teams to easily navigate, configure, and manage the system. A user-friendly dashboard can enhance the efficiency of security operations.
4. Advanced Analytics and Machine Learning
Look for SIEM platforms that incorporate advanced analytics and machine learning capabilities. These features can enhance threat detection, reduce false positives, and improve overall security effectiveness.
5. Cost and Licensing
Consider the lifecycle cost (licenses, rollout costs, and ongoing upkeep) and assess whether the vendor’s pricing model aligns with the organization’s budgetary limits and operational needs.
Best Practices for Deploying SIEM Platforms
1. Define Clear Objectives
Before deploying a SIEM platform, organizations should define clear objectives for what they want to achieve. This includes identifying specific security goals, compliance requirements, and incident response capabilities.
2. Plan for Data Sources
Determine which data sources will be integrated into the SIEM platform. This may include logs from servers, network devices, applications, and cloud services. A comprehensive data collection strategy is essential for effective monitoring.
3. Implement a Phased Approach
Consider implementing the SIEM platform in phases to minimize disruption and allow for gradual adjustment. Start with critical data sources and gradually expand to include additional systems and applications.
4. Train Security Teams
Provide training for security teams to ensure they are familiar with the SIEM platform’s features and capabilities. Proper training can enhance the effectiveness of the platform and improve incident response times.
5. Regularly Review and Update
Continuously review the SIEM platform’s performance and effectiveness. Regularly update configurations, rules, and alerts to adapt to evolving threats and organizational changes.
Conclusion
SIEM platforms are vital components of modern cybersecurity strategies, offering organizations the ability to detect, respond to, and mitigate security threats effectively. By carefully evaluating SIEM solutions and following best practices for deployment, organizations can enhance their security posture and ensure compliance with regulatory requirements. As cyber threats continue to evolve, investing in a robust SIEM platform is crucial for safeguarding sensitive data and maintaining operational integrity.
Explore our “Technology” category for more insightful content!
Don't forget to check out our previous article: Digital Signatures: Ensuring Legality & Security in Transactions